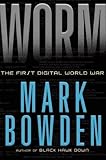
Worm :
by Bowden, Mark,
Edition statement:1st ed. Published by : Atlantic Monthly Press, (New York :) Physical details: x, 245 p. ; 24 cm. ISBN:9780802119834; 0802119832. Year: 2011| Item type | Current location | Call number | Copy number | Status | Date due | Barcode |
|---|---|---|---|---|---|---|
 Books
Books
|
National Centre for Radio Astrophysics
Welcome to NCRA- WEB OPAC |
681.324 BOW (Browse shelf) | 16207 | Available | 16207 |
Browsing National Centre for Radio Astrophysics Shelves , Shelving location: General Stacks Close shelf browser

|

|

|

|

|

|
No cover image available | ||
| 681.324 / NOB Building Modern Networks | 681.324 ALL Network maintenance and troubleshooting guide : | 681.324 BLA Computer networks : | 681.324 BOW Worm : | 681.324 CHE Firewalls and Internet security : | 681.324 FAD Unofficial guide to ethical hacking / | 681.324 GRA The handbook of personal area networking technologies and protocols |
Includes bibliographical references.
Zero -- MS08-067 -- Remote thread injection -- An ocean of suckers -- The X-men -- Digital detectives -- A note from the trenches -- Another huge win -- Mr. Joffe goes to Washington -- Cybarmageddon -- April fools.
Journalist Mark Bowden delivers a look at the ongoing and largely unreported war taking place literally beneath our fingertips. When the Conficker computer worm was unleashed on the world in November 2008, cybersecurity experts did not know what to make of it. Was it a platform for criminal profit, or a weapon? The worm, exploiting security flaws in Microsoft Windows, grew at an astonishing rate, infecting millions of computers around the world within weeks. Once the worm infiltrated one system it was able to link that system with others to form a single network under illicit outside control, a situation known as a "botnet," soon capable of overpowering any of the vital computer networks that today control banking, telephone service, energy flow, air traffic, health-care information, even the Internet itself. This book reports on the battle between those determined to exploit the Internet and those committed to protect it.--From publisher description.
There are no comments for this item.